Recently it was reported (http://www.scmagazine.com.au/News/305227,linkedin-adds-salting-after-password-scare.aspx) that LinkedIn (www.linkedin.com) has a breach and it is speculated that over 6 million passwords were compromised. A file containing 6,458,020 SHA-1 unsalted password hashes was posted and can be cracked, although associated email were not found. Network security is a challenge for even such a large and well-funded company such as LinkedIn. Obviously everyone on LinkedIn should be changing passwords. Although the data which has been released so far does not include associated email.
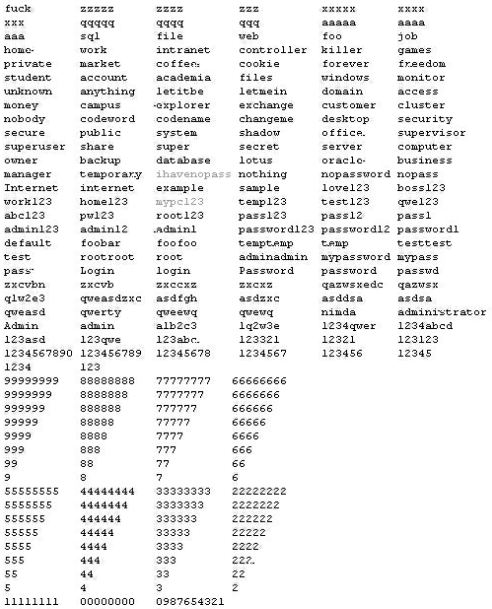
LinkedIn has subsequently confirmed the compromise and that a majority of the stolen passwords have been cracked. From the list cracked, it’s easy to see why it’s easy to crack passwords as users frequently user very simple passwords.
Check out one of the many password crackers, Cain and Abel http://www.oxid.it/cain.html
LinkedIn has since changed the passwords to be stored in salted hashed format, which means a string is added to the password before it is hashed and harder to crack.
Passwords are usually used across multiple logins. Most users do not use unique passwords across 10 or 20 or 30 logins, as that is pretty hard to remember. So assuming the passwords are cracked and email logins discovered, it can be used to leverage access to other sites. For example, is your LinkedIn email id is your company email, then with a password, perhaps an attacker can log into your Outlook Web Access email system. Vulnerability linkage works the same for password compromises.
There is no really solution from the consumer perspective when the company entrusted with securing your data is compromised. Given enough time, even a very complex password can be cracked. The response from consumers has to be demanding better security and accountability around network security by vendors.